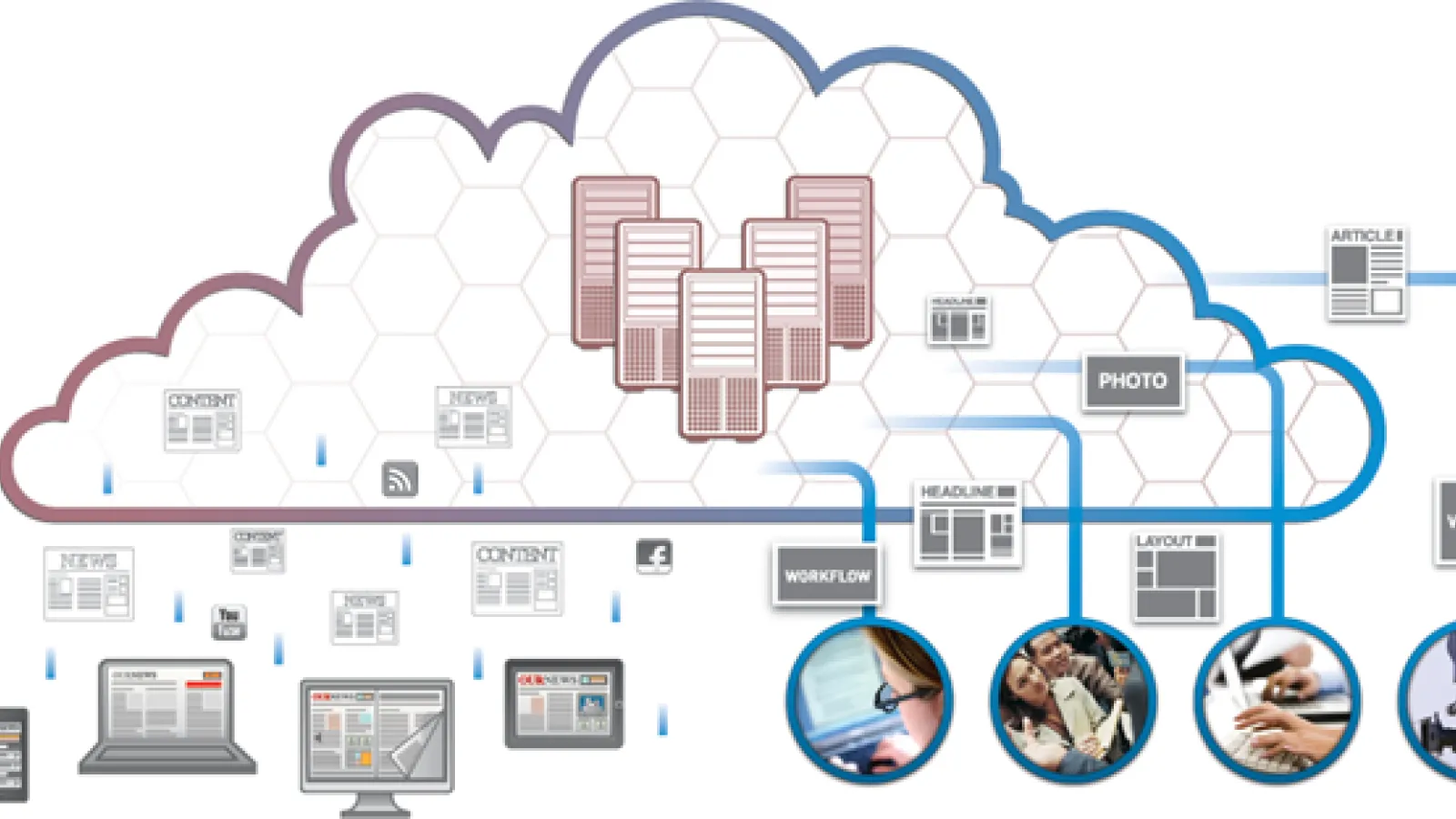
As Cloud computing garnered year-over-year traction in the enterprise world, companies have wondered if it would suit the needs of these organisations and if it is as a matter of fact doing today, how smooth would the transitions be. For over a series of articles we have been exploring and touching the areas that require the most of the attention when it comes to Cloud Computing Technology for the Media and Publishing houses.
In this latest article we plan to cover the summarized version of the previous articles and sum it up. Starting from the first article, we have explored 4 areas to begin with.
We have understood,
#1 What do Publishers’ have on their plate?
Streamlining it to the main categories
- Enhancing experience for the consumers
- Increase Revenue without compromise in business
- Manpower Cost cut down
We have discussed that whether Cloud can be a solution to a particular firm will depend on the way the business and technology is. Each each Media and Publishing enterprise function differently and Cloud computing will not necessarily be a game changer on its own. But together with the integration and experimentation will emerge out to be one of the forerunners in scalability and match the speed with which consumers are absorbing experience.
#2 Who uses Cloud?
Discussed some of the big names in Media associated to Cloud - Time Inc.
#3 What benefits can Cloud provide?
- Handling disruptions
- Handling traffic demand
- No infrastructure maintenance
- Improve infrastructure without people
- No people maintenance
- Reduced Software Costs
- Improved and Fast updates
- Unlimited storage space
- Worldwide accessibility without costs to set up data center
Understood,
#4 Different Cloud Technology Stack
Iaas - Infrastructure as a Service
Paas - Platform as a Service
Saas - Software as a Service
Discussed,
#5 Security issues with Cloud
Cloud computing vulnerabilities
When deciding to migrate to the cloud, we have to consider the following cloud vulnerabilities:
- Session Riding
- Virtual Machine Escape
- Reliability and Availability of Service
- Insecure Cryptography
- Data Protection and Portability
- CSP Lock-in
- Internet Dependency
Cloud computing threats
Before deciding to migrate to the cloud, we have to look at the cloud security vulnerabilities and threats to determine whether the cloud service is worth the risk due to the many advantages it provides. The following are the top security threats in a cloud environment:
- Ease of Use
- Secure Data Transmission
- Insecure APIs
- Malicious Insiders
- Shared Technology Issues
- Data Loss
- Data Breach
- Account/Service Hijacking
- Unknown Risk Profile
- Denial of Service
With a brush up in understand the above points, we have summarized whatever we have discussed in the series of articles that we have been seeing from last week. For the next and the last article we plan to bring up a comparison of the companies that are offering Cloud Computing services to these organizations.
For further reads :
http://www-935.ibm.com/services/multimedia/fr_FR_Cloud_Computing_for_Media.pdf
http://cloud-computing.tmcnet.com/
Image Credit : http://blog.udn.com/jason080/9401738
Disclaimer: Screenshots, logos and other identification used in this article belong solely to the companies they represent.