Drupal Security Audit is a systematic evaluation performed by authorized individuals or teams or tools to identify potential security weaknesses in a system or website. The audit encompasses a comprehensive range of activities, including code analysis of the core, plugins, and modules, configuration assessments, evaluations of business logic errors, and more. The goal of the audit is to identify any vulnerabilities and provide recommendations for remediation to ensure the website's security.
Importance of Undertaking Drupal Security Audit and Penetration Testing
Drupal sites are susceptible to threats such as Cross-Site Scripting (XSS), Denial of Service (DoS), Code Execution, SQL Injection, HTTP Response Splitting, and others. Small and medium-sized businesses are the most vulnerable, with 43% of data breaches targeting this segment.
Hence, investing in a comprehensive security solution, such as Drupal Security Audit and Penetration Testing, is a wise choice because it helps to identify potential vulnerabilities and provides an opportunity to fix them before they can be exploited by cybercriminals.
In this blog, we shall concentrate on providing an overview of the specific Drupal module versions used to conduct Drupal security audit, as well as the relevant PHP and JavaScript libraries employed during the Drupal Site Audit (Fig. 1).
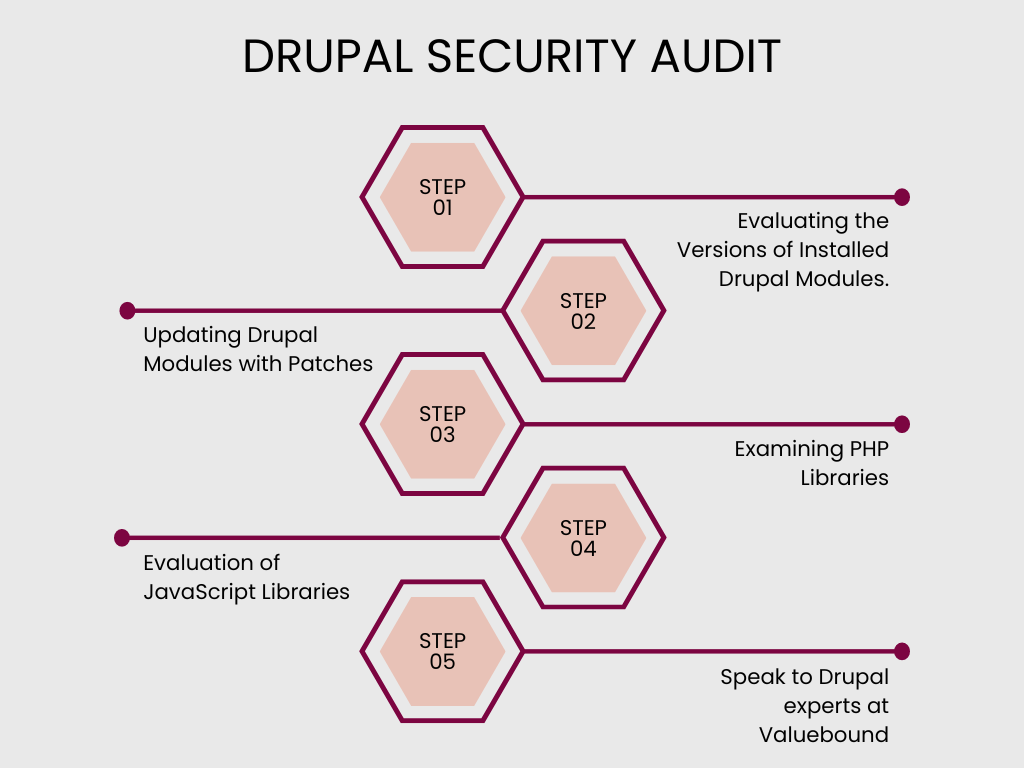
Evaluating the Versions of Installed Drupal Modules
Drupal offers a view that displays all installed modules and provides information on their update status, including the presence of any security fixes in the latest version.
In the context of Drupal, information regarding potential security flaws in a module is made public once the author releases a patched version. While the author may attempt to conceal the exact code changes made to address the security issue, this only serves to prolong the time an attacker requires to find and exploit the vulnerability. Given the significance of time in such situations, it is imperative to keep track of security updates on a regular basis, not just during a Drupal security audit.
At Valuebound, we strongly advocate for the regular updating of all available modules. The presence of security fixes in a module update is critical in maintaining the robustness and security of the application.
Updating Drupal Modules with Patches
When updating Drupal modules, it is imperative to verify if a patch has been applied to a specific module. In such scenarios, we follow these steps:
- Examination of the origin of the patch: Our first step involves checking if the patch was created by the Drupal community and if it addresses a specific issue reported on drupal.org. If so, Valuebound’s Drupal Site Audit tool investigates the corresponding issue that the patch addresses.
- Latest Version of the Module: If the patch has been integrated into a newer version, we recommend updating the module and removing the patch. The code that addresses the security flaw or adds the required functionality is already present in the official, updated version of the module.
- Updating and Testing: If the patch has not yet been incorporated into the latest version of the module, we recommend updating and testing the updated version of the patch.
- Custom Project Code: In cases where the patch is not a product of the Drupal community but is instead the result of project-specific work, updating the module is still recommended. However, the responsibility of ensuring the correct operation of the patch rests with the individuals responsible for the custom project code.
After updating, it is essential to verify the functionality of the patch and introduce appropriate fixes, if required, to ensure its proper operation on the latest version of the module.
Examining PHP Libraries
In the next phase, the utilization of PHP libraries will undergo a comprehensive evaluation. This can be achieved by utilizing the "composer show" command or the "local-php-security-checker" package. The latter option is more advisable as it streamlines the process.
Drupal Composer Security Checker incorporates the security-checker package. However, the effectiveness of this module is limited, and the security-checker package itself has not been actively maintained since January 2021. As such, the "local-php-security-checker" package is the preferred option.
In the event that any security vulnerabilities are detected, it is recommended to promptly update the relevant library to maintain optimal security. Regular assessments of PHP libraries, similar to Drupal modules, should be integrated into a comprehensive security program.
Evaluation of JavaScript Libraries
The subsequent step in the process entails a comprehensive assessment of the utilized JavaScript libraries to verify their current status and the presence of security fixes. This can be achieved by conducting an inspection of both the library directory and the relevant package.json files.
For the library directory, a manual review of the version is required. On the other hand, the npm-audit command can be used to analyze the package.json files. The npm-audit command provides a comprehensive report of all identified vulnerabilities, including the threat level, the affected packages and dependencies, the package path, and a link to additional information about the vulnerability.
In the event that a vulnerability is detected, it is recommended to promptly perform an update. Regular scans of the JS libraries are encouraged and should be conducted more frequently than a full security audit.
Conclusion
Acquiring the information presented in this article represents a simple and effective method for enhancing the security of your application.
The first step in a comprehensive security audit, conducted by our team of Drupal experts at Valuebound through the Drupal Site Audit Tool, involves reviewing the versions of the solutions in use. Our team highly recommends regularly checking for updates, and promptly updating whenever a security patch becomes available.
For those seeking assistance with a comprehensive Drupal security audit to assess readiness for Drupal 10, reach out to us.